Home

The Possibilities of Renewable Propane
Posted on March 13, 2024
With Low Carbon Fuel Standards, Clean Heat Standards and similar laws under…
Propane Can Do That
Posted on March 12, 2024
Take Action and Take Control of Your Future at Industry Summit VI and Visions ‘24
Posted on March 11, 2024

Redefining Zero
Posted on April 17, 2024
NEFI Responds to EERE Definition of Zero Emissions Building
RINs and Repeat
Posted on March 12, 2024
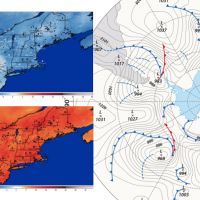
ISO NE – Not Ready for Prime Time?
Posted on March 11, 2024
U.S. DOE Releases Home Energy Rebate Guidance
Posted on September 14, 2023

Optimizing Operations
Posted on February 12, 2024
Best practices for terminal and fuel transport operators
National Weather Forecasting Takes NEFI by Storm
Posted on December 8, 2023
A Chance Hydrogen Discovery
Posted on December 7, 2023
Winter 2023-2024 First Impressions
Posted on October 11, 2023

NORA Net-0 Home Update
Posted on October 6, 2023
The need to lower carbon emissions has driven many industries to find alter…
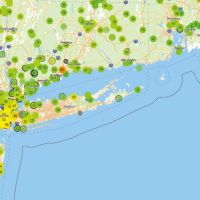
Building Your Information Network with Propane Tank Monitors
Posted on August 11, 2023
A Recipe for Delivery Efficiency
Posted on August 11, 2023
Don’t Ignore the Storage Capacity You Already Own
Posted on July 18, 2023
Burner Questions? The Answer Is in Your Hands.
Posted on April 17, 2024
Manufacturers provide step-by-step guides for new B100 burners
Carlin Begins Production on UL Listed B100 Burners
Posted on December 7, 2023
NORA Looks at Indoor Air Quality
Posted on December 7, 2023
Why Market Renewable Propane for Your Business?
Posted on October 6, 2023
A Smart Hedging Strategy Can Withstand Market Forces
Posted on April 17, 2024
The Four Key Metrics of Your Hedging Strategy
Posted on March 12, 2024
Market Forecast: What to Watch
Posted on February 12, 2024

Show Your Work
Posted on April 17, 2024
Use online GHG calculators to help prove your value to the community
Beyond the Gateway
Posted on March 12, 2024
Fill Your Idea Parking Lot for 2024
Posted on February 12, 2024
Known Knowns and Unknown Unknowns
Posted on December 7, 2023

The Imperative of Cloud-Based Data Security
Posted on April 17, 2024
Cloud-based solutions offer greater security, scalability, and access than …
Innovative Financing Solutions for Energy Businesses
Posted on March 12, 2024
Service, Support and Collaboration Separate Payment Partners From a Payment Processor
Posted on March 12, 2024
Heating Things Up: How Influencer Marketing Will Ignite the Oil Heat Industry
Posted on March 12, 2024
Join Our Email List For Updates!
Enter your email to receive important news and article updates.
Industry Prices